A quick recap on our contributors
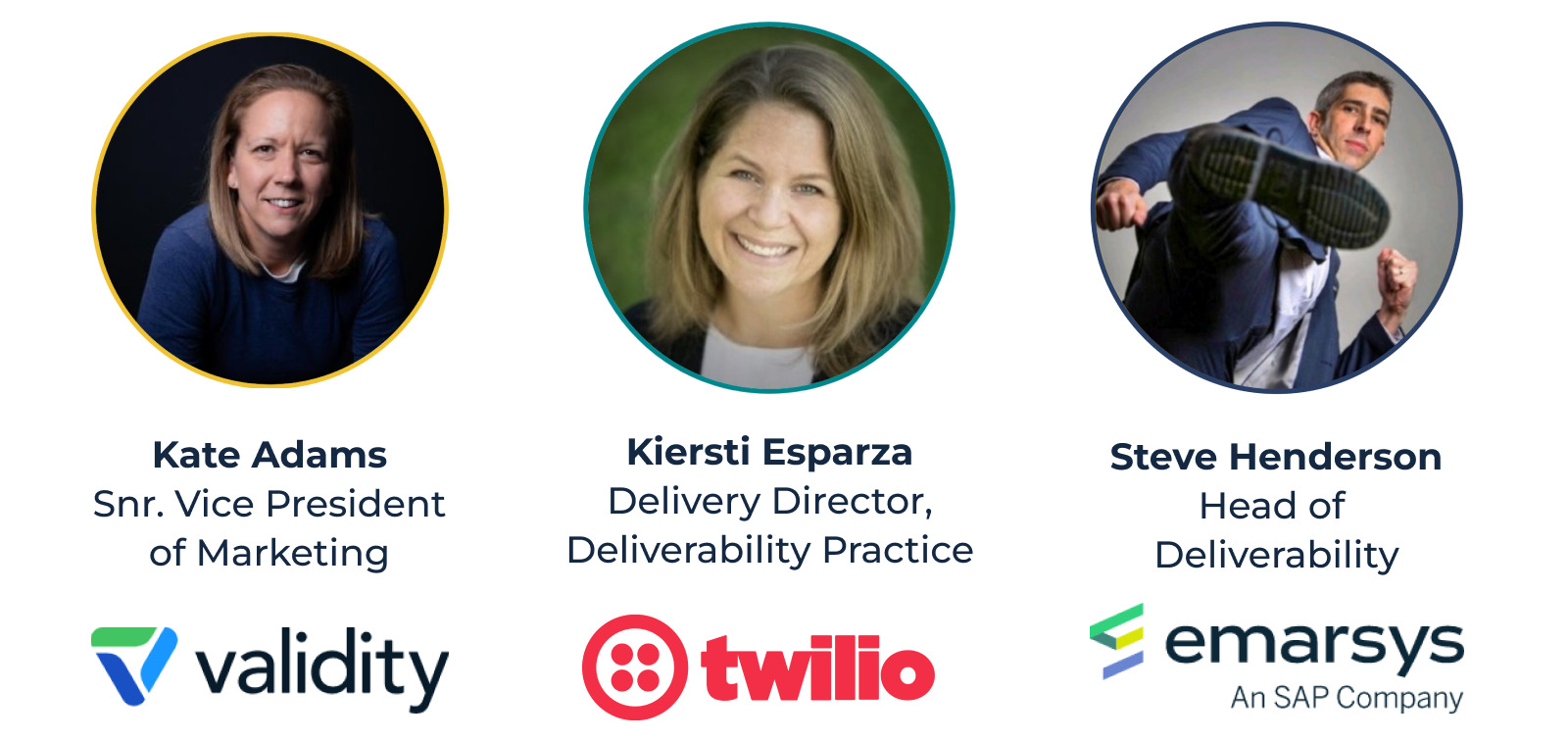
Between Kate, Kiersti, and Steve, there is approximately 50 years of deliverability experience. Safe to say, we’re in knowledgeable hands! They’re contributing to our Deliverability 101 series to help senders know, understand, and adopt best practices – if you’d like to find out more about our contributors read more in our previous blog post.
Let’s kick things off – why would a sender want to change ESP?
There are two legitimate reasons in the eyes of our experts. The most common is senders who’ve outgrown their ESP and require a more complex product. That could be a product that supports a marketing automation function instead of a batch and blast approach. “Maturing an email program in this way is encouraged,” shares Kiersti.
Equally, ESPs all manage their networks differently. If a sender is using a provider, who does not meet their requirements for compliance practices, responsible IP pooling, or lack of strong problem identification and resolution-handling identification and resolution, finding a new ESP would be a sound choice.
That said, if deliverability is the reason for considering a change, the experts would fervently encourage you to rethink. Changing ESP will not fix deliverability; the sender holds the ace card here (more on this in our previous blog post). So changing ESP will only prolong the issue, with a lot of hard work in between. Instead, you should rethink your sending practices. Discover sending fundamentals here.
What considerations should senders be aware of when migrating to a different ESP?
When you start with a new provider, you need to build your reputation from scratch. Reputation can’t be transferred. Much like in real life, you need to build your email reputation over time.
Steve explains: “When a sender changes platform, they send emails from a new IP range and a new from address. The emails may look the same on the face of it, but they have a different template and structure underneath the hood. How can an email filter decide if this is genuine or attempted abuse?”
You need to mitigate this challenge and enable filters to differentiate you quickly and easily from a malicious sender pretending to be you. How?
Authenticate, authenticate, authenticate!
“Ensure your sender domain and IP are correctly authenticated and configured,” shares Steve. Set up and test your DNS records, including Reverse DNS, SPF, DKIM, and DMARC. Without this, there is no way for an email receiver to verify that an email’s sender is who they say they are – you can read more on this here.
Think big, but start small!
Warm-up your IPs and domains by introducing low volume, controlled sends over time. “Start by sending small, routine amounts of emails to your most engaged subscribers. Gradually increase these numbers until you’re sending to the full list” notes Kate. “Using best data and a good email campaign to generate positive email engagement proves to the filters that you are to be trusted” adds Steve.
There’s a good reason for email filters being suspicious of new senders – “Email activity on new IPs is often related to bad actors sending spam or fraud, so a new sender needs to methodically illustrate they are not a bad actor” observes Kiersti.
A piece of parting advice on this topic from Kate – “Remember: Growing your email program is a marathon—not a sprint. The warmup is key.”
Stick to the plan – don’t skip ahead
Sounds obvious, but after the first few emails, don’t try to skip ahead – “build volume consistently; avoid spikes or sudden changes” states Steve. If your first sends achieve good deliverability, that means the plan is working, but not to the extent you can start running your email programs as you did before. Spikey email traffic looks like a spam campaign and may result in your emails getting blocked. Grow gradually and be consistent.
Making the right decision
But before anything, really consider your motivation for moving. If deliverability is your primary driver, first review your practices around address acquisition, database maintenance, email frequency, and content. For more tips to improve your sending practices, take a look at this eBook. Or, next up you can read the ESP’s final blog with their 5 top tips for senders to achieve email deliverability.