Profit V managing abuse
On the side of profit, a registry requires as many domains as possible to be registered and operating with its TLD. Meanwhile, on the side of managing abuse, a registry needs to pro-actively work with the relevant organizations to assist in taking down malicious domains and stop bad actors from registering new ones. We don’t know precisely where the line falls between the two – it’s not our job to. Nevertheless, it is the job of our researchers and analysts to list malicious domains.
Is it, or isn’t it terminated?
.sbs recently came to our attention. We’ll be honest, at an initial glance, we thought this TLD was in the process of being terminated but quickly realized this wasn’t the case.
In November 2014, .sbs was registered with ICANN by Australia Broadcaster, Special Broadcasters Services (SBS), and yes, you can spot the birth of a TLD in that acronym! In April 2020, the broadcaster filed a termination notice with ICANN.
ICANNWiki states, “On April 22, 2020, Special Broadcasting Service submitted a Termination Notice to ICANN. ICANN is currently processing the termination request according to its procedures.” Still, since the wiki isn’t run by ICANN, we decided to dig a little deeper.
We soon discovered that .sbs was taken over by ShortDot in June of this year and became a generic TLD (gTLD). Unfortunately, even ICANN’s records appear to be a little askew as their website indicates that ShortDot’s operator agreement started on 7 November 2014 – clearly the date of the original agreement with SBS. Although, in fairness, IANA’s Delegation Record for .sbs is still showing SBS as the sponsoring organization. So, it would appear various key organizations need to update their records.
Do increased registrations need to equal increased abuse?
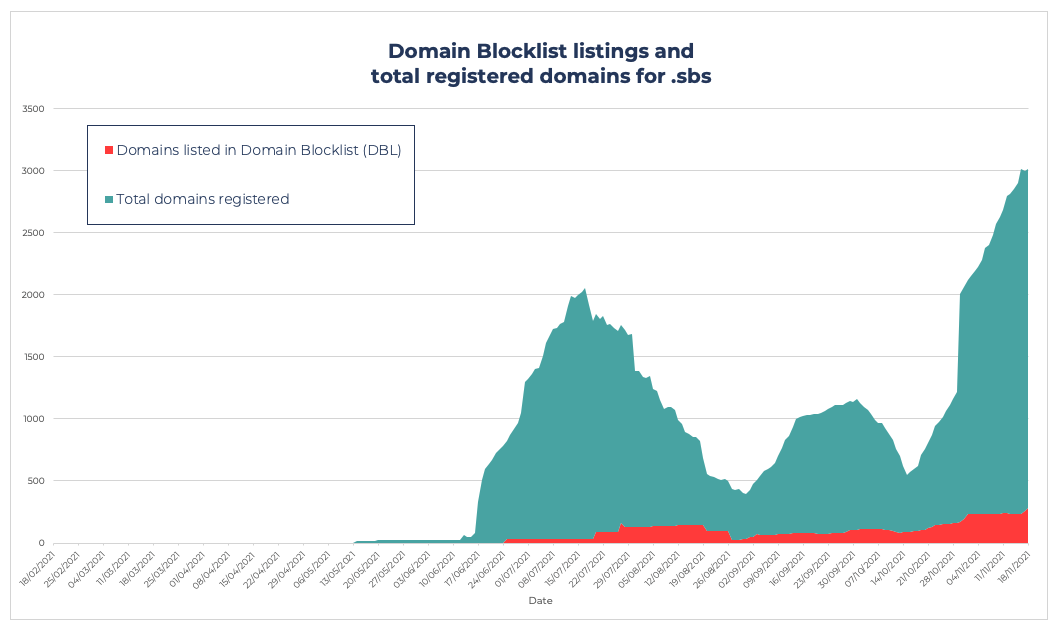
The graph below clearly illustrates how .sbs is starting to grow in popularity. The green shows the total number of newly registered domains. Unfortunately, that popularity is not only shared amongst legitimate operators, as the red in the graph shows. In the past month, our analysts listed 10% of their total registered domains. Now, in the grand scheme of things, that’s not a disgraceful percentage; after all, in the Top 10 Most Abused Top Level Domains, operators are showing rates between 19%-59%.
BUT.
(and there’s always a but, isn’t there?)
When you have, what is effectively a shiny new domain, clean and pristine, surely you want to keep it that way? Particularly, when you’re marketing .sbs to stand for “Side-by-Side“ and your value propositions is a TLD “where people cultivate unbiased mindsets” and “public interest agendas meet meaningful actions.” Surely this TLD doesn’t want to be associated with any malware?
Over the coming months, we will be exploring the world of TLDs, talking with registries, and looking at what they’re doing to fight abuse. Hopefully, .sbs keeps a lid on the amount of abuse on their TLD to match their value proposition… we’re always happy to provide advice to assist in those efforts.