Content

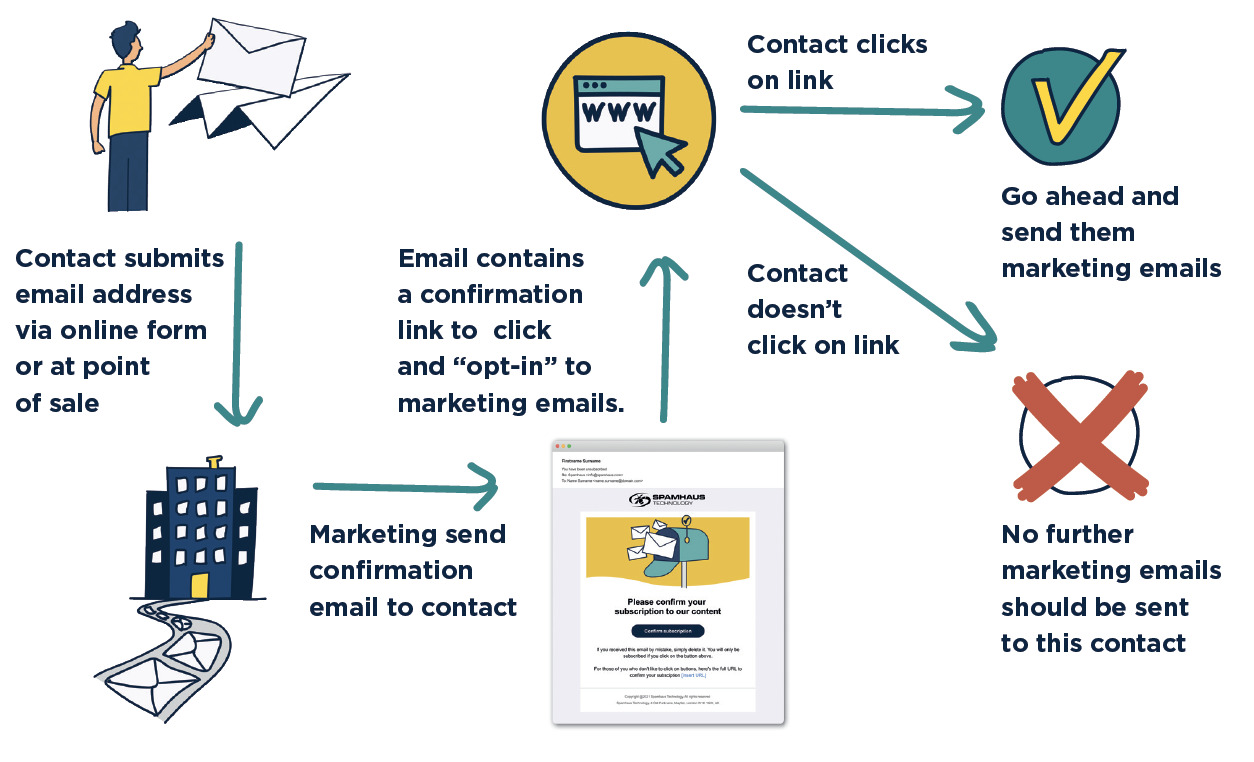
1. Confirmed Opt-In / Double Opt-in
Here is an outline of the process for confirmed opt-in (COI):
Benefits of Confirmed Opt-In
While this method requires more work and investment than others, the payoff in list quality more than offsets it.
- It increases the integrity and reputation of the sender in the eyes of the recipient.
- Happy recipients are more engaged – If you treat a recipient’s inbox and time with respect, they are less likely to report that email as spam and less likely to unsubscribe (and happy customers tend to make more purchases.)
- You won’t regularly hit spamtraps – Spamtraps do not interact with email, so you significantly reduce the likelihood of poisoning a contact list with a trap.
- You won’t risk all your emails being blocked – ISPs often block whole email streams that generate a lot of spam complaints or hit their traps, resulting in a loss of inbox delivery, reputation, and revenue.
- It makes investigations easier to resolve. When an ISP, filter vendor or reputation provider refuses a sender’s email, they often require proof of consent as part of the investigation. You can’t provide this if you haven’t sought permission and had it granted via COI. They also can require a ‘re-permissioning’ pass and demand that you offer all your subscribers the chance to opt-out or remain subscribed and that those choices must be honored.
- Confirmed opt-in provides a low-risk, high ROI method of reaching contacts.
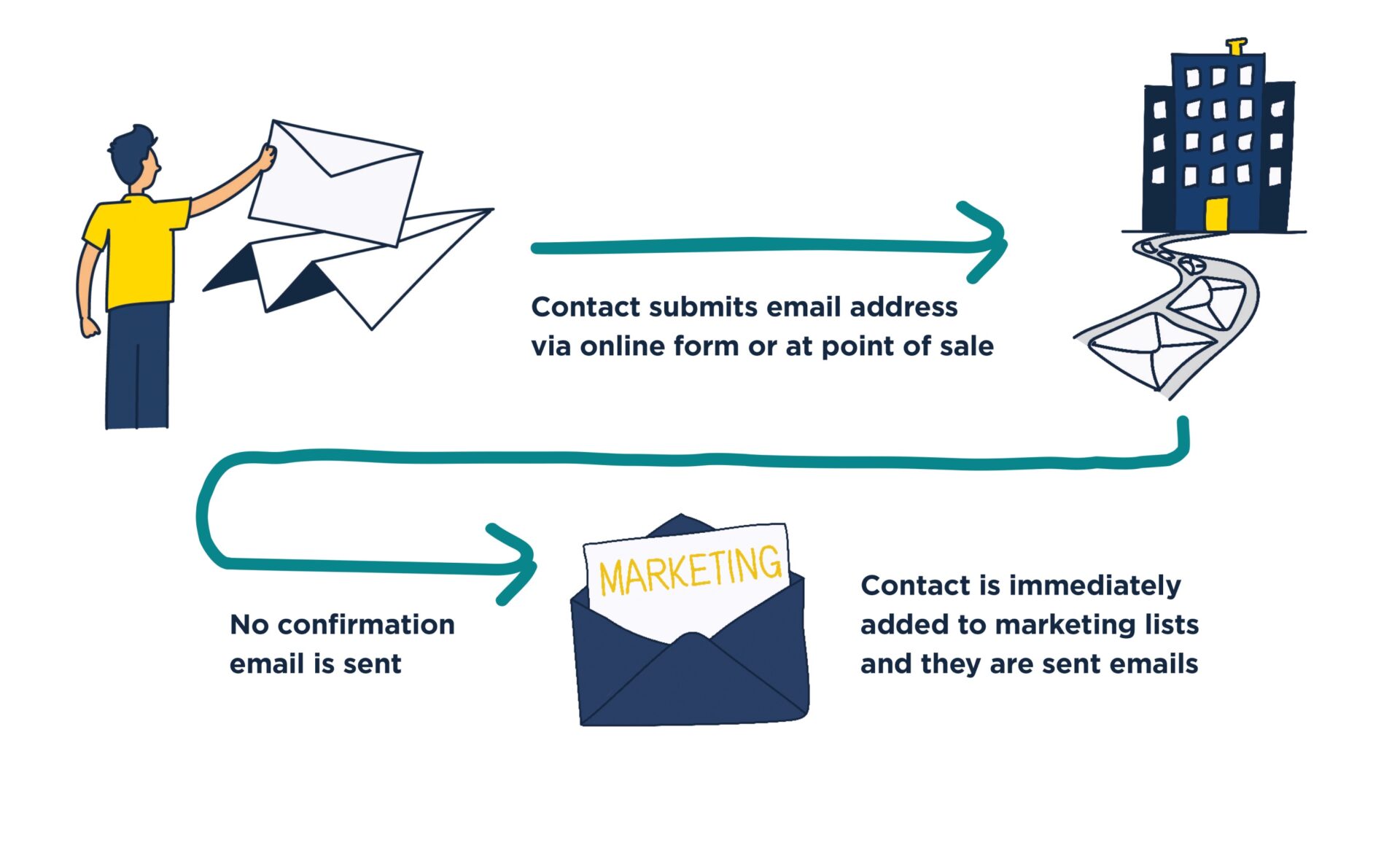
2. Opt-in / Single opt-in
This is a widely used method that involves no confirmation of consent:
Issues with single opt-in
While it is possible to run a successful email marketing campaign using this method, it can cause these problems:
- It is impossible to know if the recipient truly wants to be added to your marketing list without the recipient verifying this is the case.
- Increased risk of spam complaints. If the contact didn’t realize they were subscribing to your marketing emails and suddenly started to receive them, they may mark them as spam or make a direct complaint.
- Hitting spamtraps – if someone uses a spamtrap email address for a signup, it will poison your mailing list. Malicious submissions of spamtraps can cause tremendous difficulties, which can be very time-consuming and expensive to resolve.
- Potential to be listed on blocklists. The consequences of hitting spamtraps could be a listing on a blocklist, leading to bounces for all your emails.
- Risk of typos, bot submissions, or throw-away emails. Unconfirmed email addresses can be maliciously submitted. People often use throw-away, typod, expired, or imaginary email addresses to get what they want from a website without accepting more marketing emails.
All of these factors can poison a mailing list since user engagement is the most critical factor in determining the fate of an email today. Unexpected marketing mail causes people to report it as spam, driving down reputation and deliverability.
- Increased bounce rates – Incorrect addresses cause high bounce rates, which can (and do) provoke adverse reactions from ISPs, resulting in spam foldering, rate-limiting, or blocking.
3. Opt-out
Opt-out is the least useful, messiest, and riskiest of all acquisition methods, and you should avoid it at all costs. It has been proven to negatively affect IP and domain reputation, causing severe problems with successful email delivery.
Opt-out employs the assumption that you can acquire permission after the event: That’s not how permission works. It cannot be granted retrospectively; you must get it upon initial contact. Opt-out methods also include the use of purchased or rented mailing lists, addresses scraped or harvested from the web, etc.
Issues with opt-out
Opt-out places the burden of permission on the recipients, which rarely goes well for the marketer. Use of this method is guaranteed to cause:
- High bounce rates.
- Spam complaints.
- Hitting Spam traps.
- ISP blocks.
- Listing on blocklists by reputation and filter vendors.
Next stop… let’s move onto the day-to-day operations of running a marketing email program starting with how to avoid looking like a spammer when you’re sending emails.