Content
For at least three months, Freenom’s doors have been firmly shut to new domain registrations. You’d expect this to be nothing but good news, given their history, as highlighted in a number of our reports.
But what if you’re operating in this competitive market? It will come as no surprise to learn that domain registries are reaching out to our domain experts to understand recent negative rankings better. Coincidence? We think not.
Domain experts observe an unprecedented change
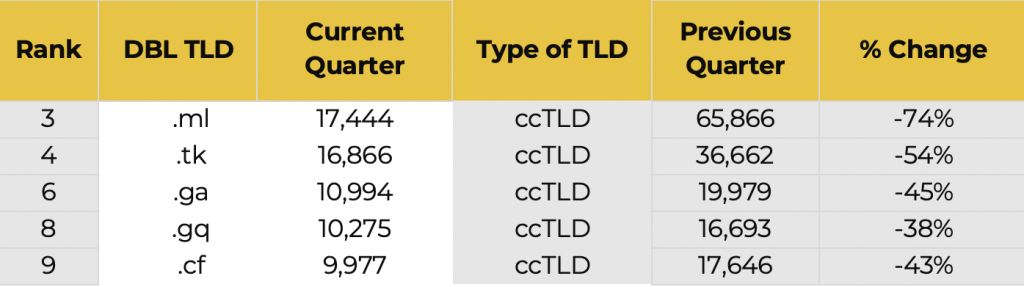
Our domain experts have never seen a change as dramatic as that of the TLD landscape over the first quarter of 2023. Yes, there are the expected fluctuations of domain registrations linked to current events, seasonal activities, or short bursts of aggressive promotion typically fuelled by speculators and abusive or highly fraudulent registrations. Yet, for the first time, Spamhaus researchers observed all five Freenom-operated TLDs dramatically decrease in abuse numbers.
Domain listings by ccTLD
This is an unprecedented change, given these TLDs have been a constant in the statistics Spamhaus reports on, relating specifically to domains associated with spam, phishing, and malware. Why the sudden change?
Freenom – when free domains become a problem
Located in the Netherlands, Freenom was the world’s first and only free domain registration service. Sounds great if you want to purchase domains, but not from our point of view. Unfortunately, free domains tend to attract the less desirable user and all their associated badness, i.e., abuse. In fact, Freenom services are well known to security experts for providing domain registration services to malware authors, botnet operators, and phishing operations.
The problematic top-level domains
In particular, are five free country code top-level domains (ccTLDS), .tk (ccTLD of Tokelau), .ml (ccTLD of Mali), .ga (ccTLD of Gabon), .cf (cc TLD of Central African Republic), .gq (cc TLD of Equatorial Guinea). Usually, domain registrants would use such ccTLDs for their applicable country or region. However, these five ccTLDs operated by Freenom, are primarily operated outside of their country, making them more akin to general top-level domains (gTLDs).
As highlighted earlier, Freenom’s TLDs have had a poor reputation for a long time across many areas of internet security. Still, the fact that miscreants could endlessly rotate through new names meant that supplies were endless. As a result, these five TLDs have experienced exceptionally high levels of abuse and, subsequently, high volumes of bad domains due to being free.
That was until this year when Freenom announced the doors were closed to new registrations. What’s most interesting is why?
Technical issues you say…
Freenom appears to be experiencing “temporary technical issues”, which have been ongoing since at least January 26th when some forum users reported the problems. Could this be a consequence of Meta’s recent court filing in March against Freenom and another (unrelated) legal case against Freenom, based in the Netherlands? It would be a reasonable assumption.
The good news remains, Freenom’s abused domain numbers are decreasing due to the fact new registrations are no longer being accepted. BUT there is a flip side to this good news; assuming Freenom continues with its “technical issues,” a change is being forced upon the operations of those who rely on access to a never-ending supply of free domains to circumvent domain-based blocking. Operators who utilized Freenom’s TLDs will need to find somewhere else for domain registrations or shut down their operations – the latter being a scenario we know is unlikely.
The Freenom Effect
In Quarter 1 of 2023, there was a noticeable shift in the percentage split between abused ccTLDs and gTLDs, with the latter increasing from 61% to 71%. Meanwhile, over the past week, proactive domain registries have been in contact due to their recent (negative) rankings on the Spamhaus Project website. With no significant change in abuse noted at their end and continued vigorous efforts to suspend abusive domains (if only all registries were so closely focused on abuse), what is the problem?
Our analysis reveals almost all the new entries in the gTLD list are or have been, heavily discounted at popular registrars in the first quarter of this year. Once again, proving that low pricing inevitably attracts abusive registrations.
Now that Freenom’s never-ending reservoir is gone (or so it seems), the alternatives for actual domains (instead of free hostnames at dynamic DNS providers) are all paid options. Therefore, if you are a registry operating a TLD at the lower end of the pricing scale, you are in a prime position to be targeted by bad actors.
For every crime solved another is underway
Looking to the future, it’s unlikely that all malicious operators who relied on these domains will disappear. Cybercrime is often profitable, and while free domains will produce the best margins, cheap is almost always a viable alternative.
As the latest domain data suggests, those registries that operate TLDs at the lower end of the pricing spectrum are significantly more susceptible to abusive registrations. We strongly advise registries and registrars to review their tools and processes, ensuring increased vigilance against a surge in registrations by bad actors for malware, phishing, spam, and other fraudulent activity.
Read ‘Troubles in Tokelau, malfeasance in Mali`… what’s happening with Freenom?‘ and access the ‘Domain Reputation Updates‘.