What is Passive DNS?
Until the introduction of Passive DNS, there was no way to retrieve the content of any DNS zone owned by other people. Why? System administrators were not keen to share them. Also, once a change was made to a DNS record, the previous details were gone forever as the new version immediately propagated across the internet… Not very helpful if you need to research all the domain names a suspect IP address has resolved to historically, and vice versa. Passive DNS resolves this issue.
Where does Passive DNS data come from?
To understand where Passive DNS data comes from we need to take a closer look at the basics of DNS. Passive DNS data is generated when a cache miss takes place and the hostname is resolved by an external authoritative server, instead of a DNS resolver’s cache. When you go to look at www.example.com, if no one’s checked that website out recently, the domain name has to be resolved using external DNS queries. Take a look at the infographic below:
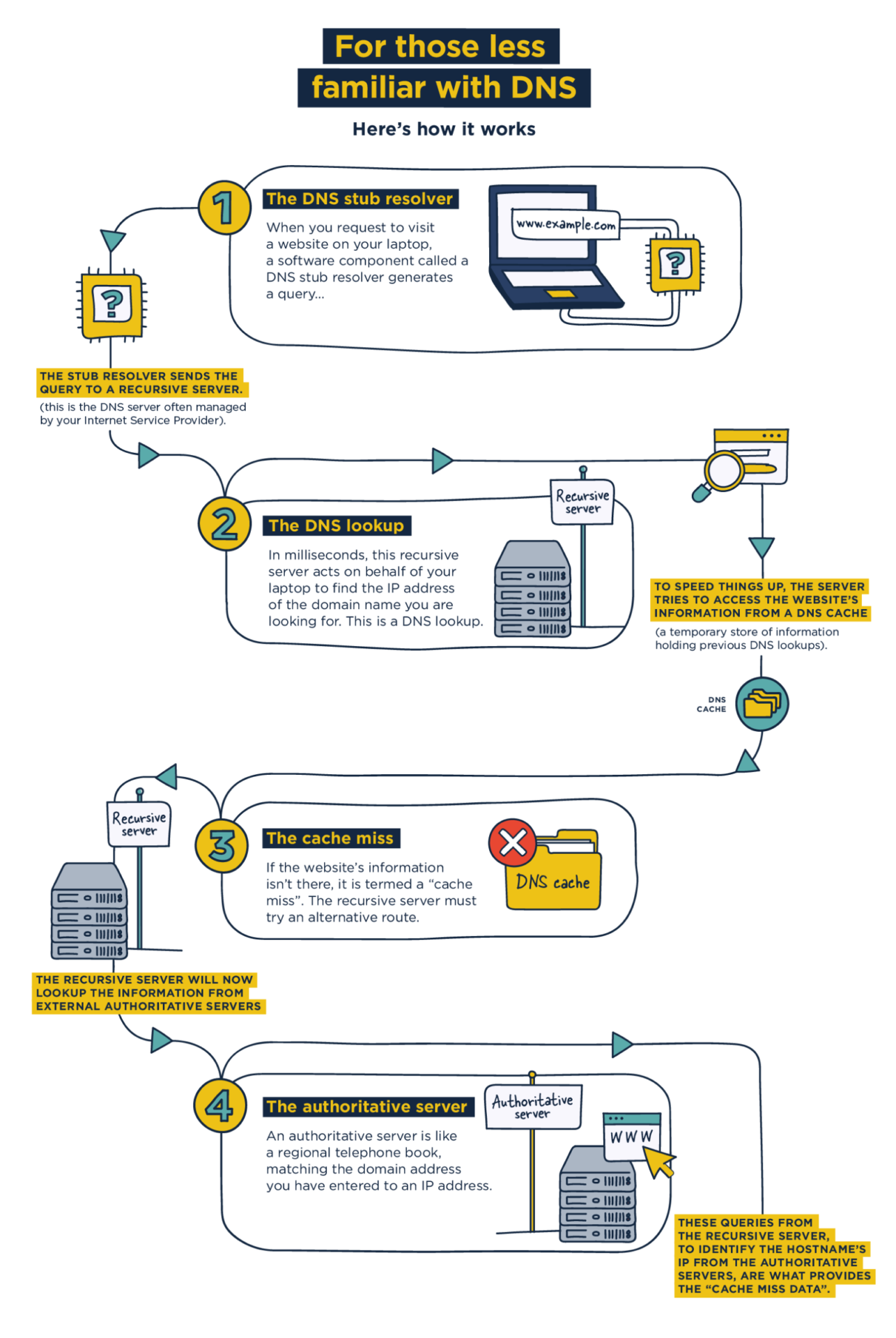
With special probes activated on the DNS resolver, after a cache miss has happened, it is possible to record the packets containing the answers to the client, along with the time & date stamp of when the query was made. This is Passive DNS data.
Does this data contain personally identifiable information (PII)?
No! All PII is held downstream. Passive DNS data does not contain which client (or person) made a query, just the fact that at some point in time, there was an association between a specific domain and a specific DNS record. Here is the exact information recorded:
- Domain name
- Record type
- Record value
- Time stamp
Privacy is maintained throughout.

Where do we collect this data from?
Passive DNS data from Spamhaus is collected across the internet globally from trusted third parties, including hosting companies, enterprises, and ISPs.
Spamhaus’ Passive DNS cluster handles more than 200 million DNS records per hour and stores hundreds of billions of records per month, providing you with access to a vast lake of threat intelligence data.
How can this help your IT security?
Passive DNS data can improve existing threat intelligence data streams, increasing visibility across potential threats. It provides a wealth of DNS-focused information for IT security teams, research teams, and brand protection specialists.
Research analysts can gain insight as to how a particular domain name changes over time and how it is related to other domains and/or IP addresses. For example, where this typically static data is suddenly changing rapidly, and a hostname’s IP address changes every 30 seconds, this indicates malpractice and requires further investigation. Passive DNS data enables you to build a picture of potential threats across global networks that cannot be identified by monitoring your network.
Brand protection specialists can identify spoofed domains/websites, noting when they have been active and how they are associated with other domains.
Discover the value this data can bring. Sign up for a FREE Passive DNS trial here.