False economy
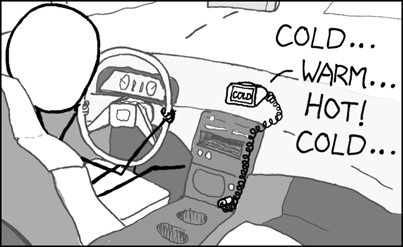
Recently I was introduced to xkcd.com by a colleague – it’s simplicity and comedic value is genius, check-it out. Upon browsing through the archive, I happened upon this little gem:
Cheap GPS
This got me to thinking about a phrase my mother drilled into me as a child “Buy cheap, buy twice.” It turns out my mother was right (again), and despite knowing this, sometimes I still can’t resist a bargain. Recently I purchased a ‘reconditioned Apple BlueTooth keyboard’ at a fraction of the cost of a new one. However, over the past few months, I’ve watched the letters rapidly fade off the keys. It’s a good thing that I can touch type; otherwise, this article would have looked like ‘thod’ [sic].
But it’s not only cheap keyboards that are a false economy. If you’re currently reading this and considering a more ‘economical’ blocklist (DNSBL), make sure you’re comparing apples with apples; otherwise, you’ll soon have forgotten the ‘mark-down’ price, in light of the problems the poor quality of data, or service, is causing you.
Here are some questions you should be asking your blocklist provider to ensure you’re getting quality for less:
1. How many mailboxes do your blocklists protect?
A simple way to check how trusted the provider’s data sets are is to ask how many mailboxes their current blocklists/DNSBLs are protecting. As a benchmark, Spamhaus currently protects 3 billion mailboxes every day, 365 days a year.
2. What is your catch rate?
Find out the amount of email-borne threats that are blocked by the data sets you’re considering purchasing. Ensure an independent source verifies this figure; for example, Virus Bulletin.*
3. How reliable is your service?
There’s no point in purchasing quality data if you’re going to have latency issues. Spamhaus has 80+ commercial mirrors distributed around the globe, ensuring our data is always available at low latency, no matter where in the world you are located.
4. What is your false-positive rate?
False positives create issues for your customer/user base. The knock-on effect is an increase in the amount of inbound traffic your help desk has to deal with. Ultimately this creates additional ‘noise’ for your team and pushes up your resource costs.
5. How are false positives remediated?
Establish what the process is for remediating a false positive, as and when it does occur. Does the process comply with the Internet Research Task Force’s (IRTF) best current practices, as detailed here. Is the cost borne by the block list provider or you?
6. How will I receive the blocklist data?
There are several ways data can be transferred from your provider to you. Ensure you will be receiving the updates in as near to real-time as possible.
7. How broad is the data from which the blocklists are compiled?
Data sets should be based on a broad range of data from independent sources. These should include numerous sectors ranging from Internet Service Providers (ISPs) to Enterprise businesses, in addition to in-house spam traps and honey pots.
8. How is your data produced?
The threat landscape changes at an incredible speed, so one approach/system does not cut it. Your provider must have multiple engines backed up by a team of dedicated and experienced spam researchers. Techniques including machine learning, alongside heuristics and manual investigations should be utilized.
Remember; it’s quite easy to produce a blocklist. However, to do so for decades with consistently high catch rates and low false positives requires commitment, processes and people.
9. Are you going to be asked to purchase additional hardware or software leading to capital expenditure?
Some providers focus solely on supplying threat intelligence data. This data is plugged directly into your existing infrastructure, with no extra costs. However, others may require you to purchase additional hardware or software leading to capital expenditure.
10. Will the data be tailored to the specific campaigns targeting my company and customers/users?
Ask your potential provider how they can make the data you receive from them more relevant to the threats you are being subjected to.
Happy shopping!
* SpamAssassin and the Data Query Service (DQS) blocked 99+% email-borne threats in VB Tests.