Let’s get to know fTLD and .bank a little better
fTLD Registry was granted the right to operate .bank in 2014, and .insurance a year later. Its mission is to run trusted, verified, more secure, and easily identifiable online locations for banks, insurance companies and producers, and their customers.
Security requirements for these TLDs were written together with the financial industry, ensuring they were relevant and applicable. Even today, fTLD continues to engage with a working group to review and stay one step ahead of the evolving threat landscape.
All .bank and .insurance applicants undergo a thorough verification process before being awarded a domain and must comply with strict registry policies ensuring ongoing compliance with fTLD’s Security Requirements.
How to get hostname transparency?
Needless to say, monitoring registrants’ digital assets is paramount for fTLD to maintain this high level of security. One element is ensuring that every hostname set up by a registrant is compliant; for example, an A or AAAA record is correctly set up in the DNS. The issue fTLD experienced was how to identify all the hostnames existing within their zones, to be able to pass them onto a third party for testing.
fTLD initially considered the option of convincing registrars to set up access to transfer zones with AXFR. This would have involved a complete zone transfer, including all subdomains. There were multiple challenges in going down this cumbersome route. Instead, they looked to Spamhaus’ Passive DNS.
How can Passive DNS help?
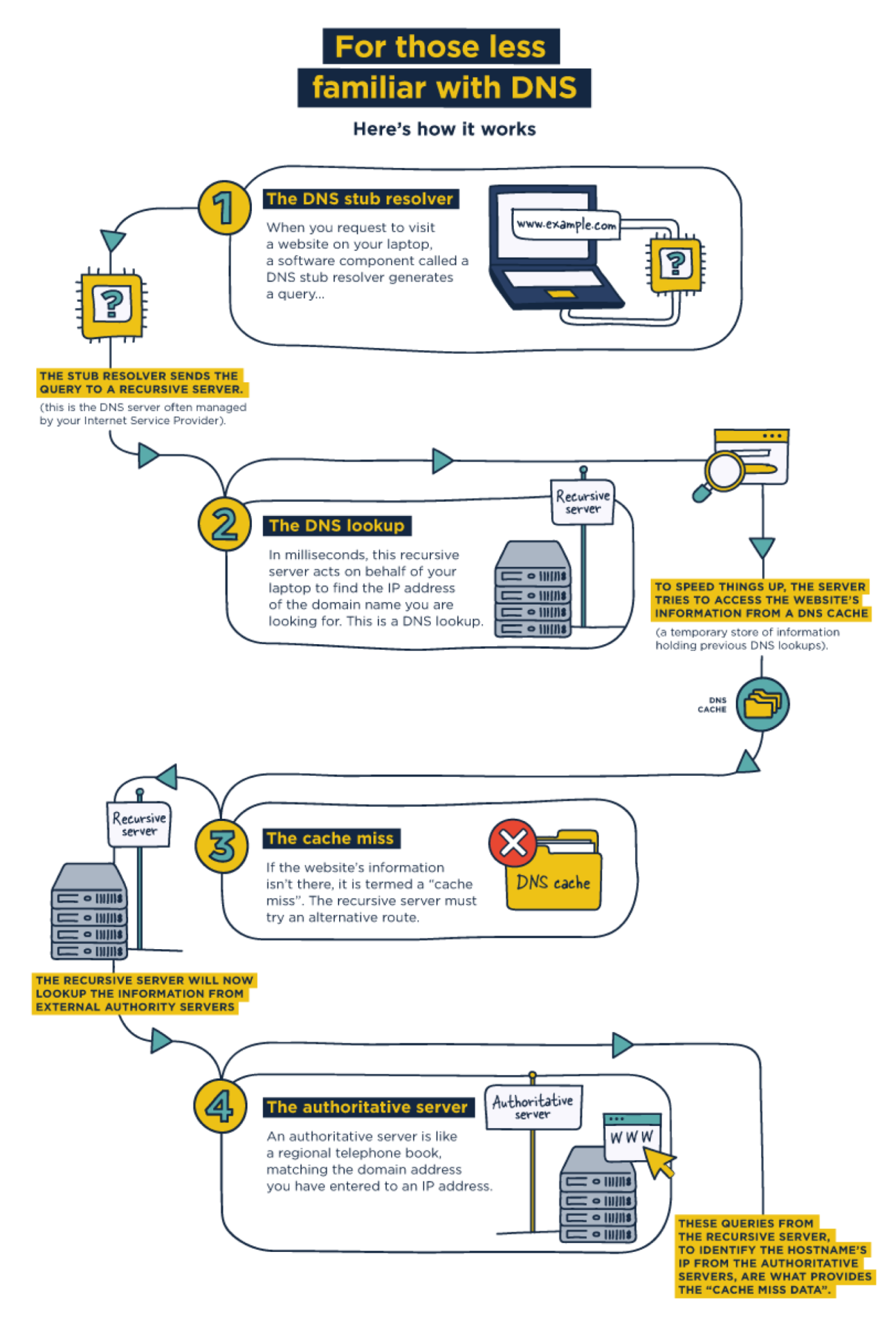
Passive DNS utilizes non-personally identifiable information (PII) relating to DNS connections when a cache miss occurs. If you’re comfortable with DNS, skip the explanation below, but if you’re less familiar, you may want to follow the arrows.
The Spamhaus Passive DNS database is vast, collecting over 200 million DNS records per hour from numerous independent organizations across the globe. Hundreds of billions of records are stored every month.
The breadth and volume of this data enable fTLD registry to search for all hostnames with the .bank or .insurance TLD. Additionally, it provides a wealth of information regarding other resources associated with those hostnames, including name servers, IP addresses, and mail exchange records. In Heather Diaz’s words, Senior Director of Compliance & Policy at fTLD, “Our system benefits from this additional data to provide more precise results.” Heather added, “it’s enabled us to discover security issues that would have been left unnoticed without this service.”
How does fTLD access the Passive DNS data?
Spamhaus’ API integration made implementation straightforward. In a typical month, fTLD executes more than 90,000 queries and processes approximately 1.2 million records from the passive DNS database.
How has Spamhaus’ Passive DNS assisted fTLD Registry?
In Heather Diaz’s words, “We needed the technical capability to listen at the root DNS of our registry system, and a zone transfer option was too complicated. Spamhaus’ Passive DNS is a great solution to enable fTLD, or any registry, a fast and simple way to analyze its zones. This was the key to implementing our compliance security monitoring solution for .bank and .insurance.”