The journey to safer email engagement
It’s fascinating that a standard that was first discussed back in 1997 is still around to this day – almost 25 years later. I’m of course talking about Sender Policy Framework (SPF) – the first attempt at mitigating spoofed emails. While SPF serves its purpose and has a pretty good adoption rate, it doesn’t solve a fundamental problem with spoofed emails. Now if you’re familiar with email, feel free to skip the next paragraph while we share an email fundamental that is important for understanding authentication.
We tend to think of email as having one sending address – the ‘From: address’. Actually, there is another address associated with each email, the ‘envelope sender’. This address is predominantly used for bounces or errors and isn’t visible by the user unless they dig into the email source code.
The challenges of the older email specifications
The problem with SPF is it only protects by assessing the ‘envelope sender’ address. This poses a big challenge. It’s the ‘From: address’ that’s far more likely to be spoofed, given it’s most visible to users, yet this address is not reviewed so users are left exposed.
It wasn’t until over a decade later, in 2012, that Domain-based Message Authentication Reporting and Conformance (DMARC) came along to tackle that problem. DMARC requires that the domain used in the ‘From’ header (that’s shown in the email client), matches with either the domain used for SPF or that the message is signed with another authentication technique, DomainKeys Identified Mail (DKIM) for that domain.
DMARC is a fantastic standard, but it has one major flaw; it is extremely difficult to implement if you have a large and complex infrastructure with a lot of different components sending email. This becomes evident when looking at adoption rates, with a large portion of the biggest brands and governments not implementing it yet.
So what does BIMI bring to the authentication party?
Clearly, even with three authentication techniques, there are still challenges with authenticating email. Enter Brand Indicators for Message Identification – or rather – BIMI. Sounds cool, but what is it?
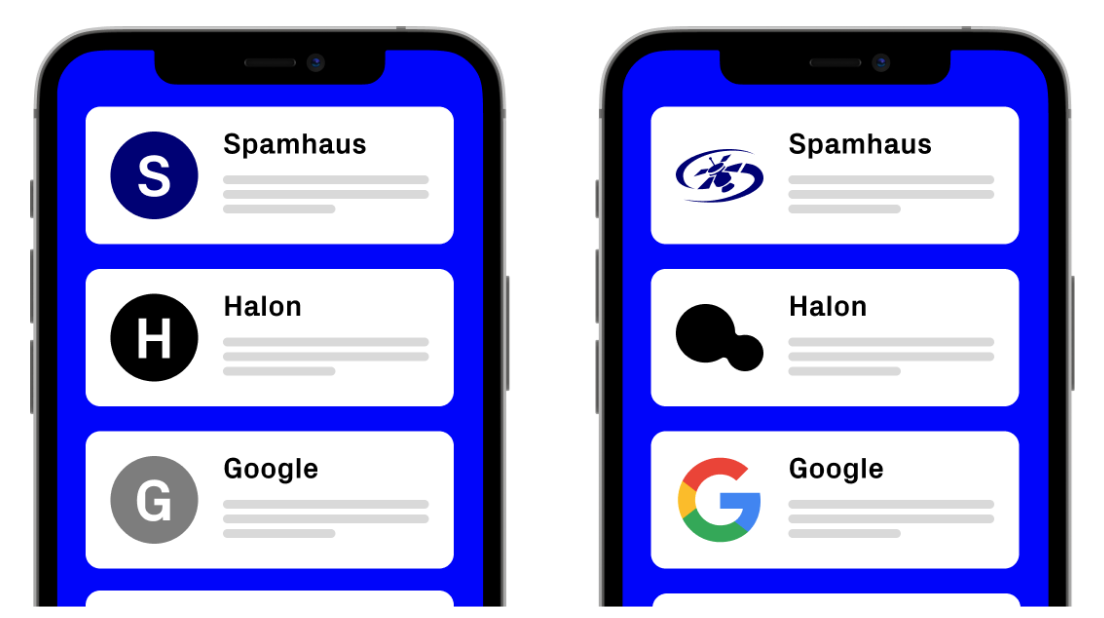
Published in February 2019, BIMI is a proposed standard (draft) that enables brands to have their logo displayed in recipients’ inboxes, to enhance the user experience. But, it’s of course more complicated than that when put into practice.
How does BIMI work?
With domains, it’s quite easy for the recipient to notice discrepancies. However, with graphics, it’s not as simple. Because of this, there needs to be a control function in place to make sure that only legitimate brands and senders are able to add graphics with BIMI. The solution for this is to use certificate authorities and require an actual purchased certificate to implement BIMI.
This certificate is called a Verified Mark Certificate (VMC) and at the time of this writing, there are only two certificate authorities that issue them: DigiCert and Entrust. On top of that, your logo must be trademarked with an appropriate authority, which, unfortunately, right now can make it a bit tricky for companies outside of the US. But that’s hopefully about to change.
And now for the kicker; BIMI requires a sender to have DMARC implemented with an enforcement policy of p=reject or p=quarantine – you can find out more on this here. No DMARC means that there is no fancy logo in recipients’ inboxes; it’s that simple. It’s pretty obvious that one of the big goals with BIMI is to increase DMARC adoption, which is very much needed.
But why are we talking about BIMI now?
It’s a pretty new standard, and it hasn’t seen a lot of adoption yet. In fact, of all the big mailbox providers right now, only Google and Yahoo support it. But that’s all about to change, with Apple recently announcing they will support BIMI in their upcoming iOS, iPadOS, and macOS releases. It is predicted that this announcement will drive more companies to push for both DMARC and BIMI implementation. If one thing is for sure, it’s that BIMI is absolutely here to stay, and it’s a great step forward when it comes to email security.
But don’t forget, it’s not just BIMI and DMARC that you should set up; SPF and DKIM still play significant roles. The folk at Spamhaus tell me you can find details on these authentication methods here. Happy authenticating!