Content

IP & Domain Blocklists (DNSBLs) are very effective at filtering malicious emails. However, they do have one big limitation: How do you block an email sent from a compromised account at Gmail, Hotmail or any other large email service provider (ESP)?
You can’t block all email from these ESPs. But, by creating a hash of a compromised email account, emails from the hacked account can be blocked, while protecting the privacy of its owner. Additionally, this approach can be expanded to cover other areas of concern that can’t be blocked based on IPs or domains.
What’s a Hash Blocklist?
In simple terms, a Hash Blocklist (HBL) is a list of cryptographic hashes derived from suspected malicious content. Spamhaus’ HBL has been designed to be extendable i.e., subsets of the list can detail different areas of malicious content. Compromised email addresses, cryptowallets, malware files and malicious URLs are all included in Spamhaus’ HBL.
Users have seen >30% of spam messages being caught by this blocklist alone – with one customer confirming it detected 873 mails with Bitcoin fraud in less than 2 weeks! When applied correctly during the post-data phase, it can be a powerful asset to protect your mail stream – so let’s take a look at how it works in more detail.
How do you block emails from compromised accounts belonging to large email service providers?
Let’s imagine a case where Vicky’s Gmail account is compromised. An attacker can use Vicky’s credentials to send an email message coming directly from Vicky. The usual ‘hooks’ used in email reputation systems won’t work because the message is coming from Gmails’ server, a legitimate server providing services to millions of people. Reviewing the reputation of the sending IP address won’t help, nor will the sending domain.
However, when Spamhaus assesses an email account to be compromised, we will associate a hash to that specific email address. This allows users to query the HBL and block emails that are coming from that hacked email account, that otherwise would have gone undetected.
How does a Malware Hash Blocklist work?
Similarly to a malicious email address, where we have seen a file to be associated with malware, we assign that file with a cryptographic hash. So, even if no malicious IPs or domains can be associated with the email message containing the malware file, the Malware HBL can be queried for that hash in the “file” context. The Spamhaus HBL return codes will tell you one of two things:
- If it’s malicious: here the queried file has been analyzed by Spamhaus Malware Labs and is recognized as known malware. The malware family is also provided in the return record.
- If it’s suspicious: here the queried file has been observed in spam, and its nature makes it suspicious. While Spamhaus Malware Labs hasn’t confirmed its maliciousness, the file still should be treated with extreme caution.
A malware file can have a hash associated with it and be listed on the Malware HBL within only 30 seconds of detection. This is as a result of our researchers’ advanced collection and agile dissemination methods.
How does a Cryptowallet Hash Blocklist work?
Think of the “sextortion” scam emails, which are currently so prevalent. You know the ones – they look something like the one below:
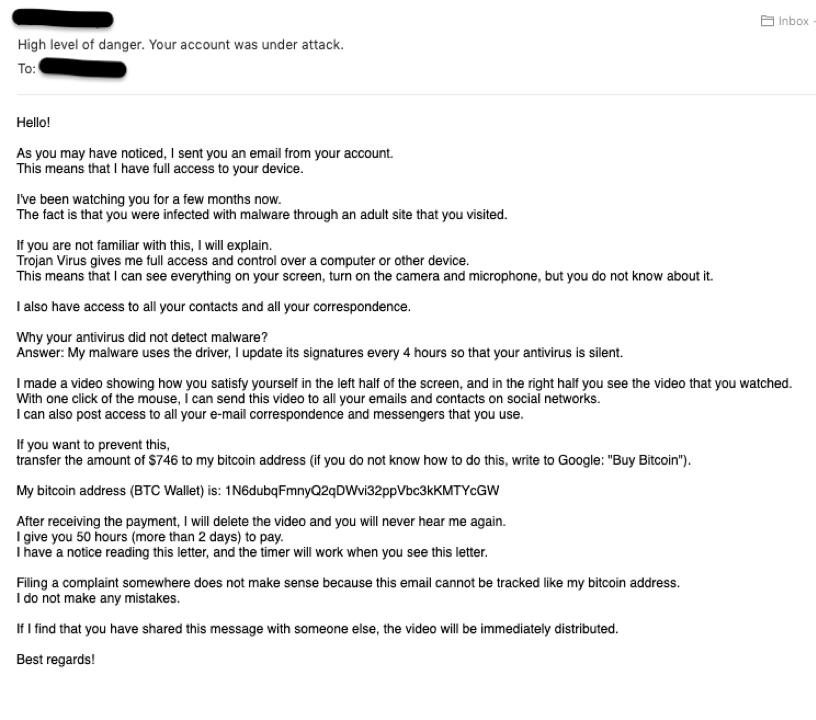
The sextortion email includes a bitcoin address of where the victim is to send money. Even if the sending email doesn’t trigger a rejection based on IP or domain reputation, the bitcoin address can be used to determine that the email is malicious in nature and result in the email being blocked anyway.
How does the URL Hash blocklist work?
The use of online file storage providers, URL shorteners, and URL redirectors to distribute malicious content is becoming ever more prevalent. Using HBL, those tasked with protecting email infrastructure can block malicious URLs without causing legitimate users of the domain to be flagged.
For example, if a malware distribution site was being hosted on https://docs.google.com/file/example_URL, if the hostname “docs.google.com” was placed on a DNSBL, the number of false positives this would create would be huge. However, by filtering on the specific URL of the malware distribution site, harmful email content can be filtered.
Whenever Spamhaus’ threat hunters determine a URL to be associated with malicious or suspicious content, they assign it with a hash. This is a unique 30+ character-string used to identify the content. And it is this unique hash that can then be used to block the malicious URL.
By querying this component of the HBL, users can block emails containing malicious URLs that otherwise would have passed undetected. This means users can query the HBL for the URL hash, even if no malicious IPs or domains are associated with the email message.
Find out more about how HBL has enhanced its protection to include malicious and suspicious URLs,
Never-ending possibilities
Virtually anything that can be extracted from an email message can be hashed. This data then can be used to create a new sub-list, thus increasing the number of reputational hooks available to you. The Spamhaus HBL helps postmasters and filtering software identify and block emerging threats now and, due to its extensible nature, well into the future.