What is Border Gateway Protocol (BGP)?
Before we kick off, it’s worth noting that BGP and BGP Firewall are different “things”. All routers “speak” Border Gateway Protocol (BGP), which is a routing protocol, or set of rules, enabling Autonomous Systems (very simply, networks having their own IP address spaces) to exchange reachability information in a standardized way with each other. This creates a common language and enables efficiency for the Internet to function.
What is Border Gateway Protocol Firewall?
In essence, it’s a protective measure to make routing as safe as possible and avoid connections to maliciousness. BGP Firewall contains feeds, or communities, that list malicious IP addresses, allowing you to block connections at the network edge in real time.
By malicious IPs, we’re talking about dedicated botnet command and control servers (C&Cs), botnet C&Cs hosted on compromised devices, or IP space that is either hijacked or leased by cybercriminals. The IPs are used to spam, host malware-infected sites, distribute phishing emails, and launch DDoS attacks against other networks.
By blocking these connections, you block already infected devices within your network from communicating with the associated botnet C&C and prevent further devices from becoming infected. In turn, you prevent spam campaigns, loss of data, and encryption by ransomware.
BGPF is an exceptionally cost-effective solution to protect your network from the worst of the worst by utilizing your existing infrastructure. Peer with either your router’s DENY table or with your traditional firewall, like CISCO.
How does BGP Firewall work?
To understand how BGP Firewall works, we need to revisit a few fundamentals relating to how Internet networking and routing work. Please note, given this is a beginner’s guide, this explanation is greatly simplified. So, for the techies and those more familiar, you may like to read on.
For a device to make an Internet connection, be that to serve up a website or, as in this case, connect to a botnet C&C server, the device must be in possession of the destination’s IP. With that IP…
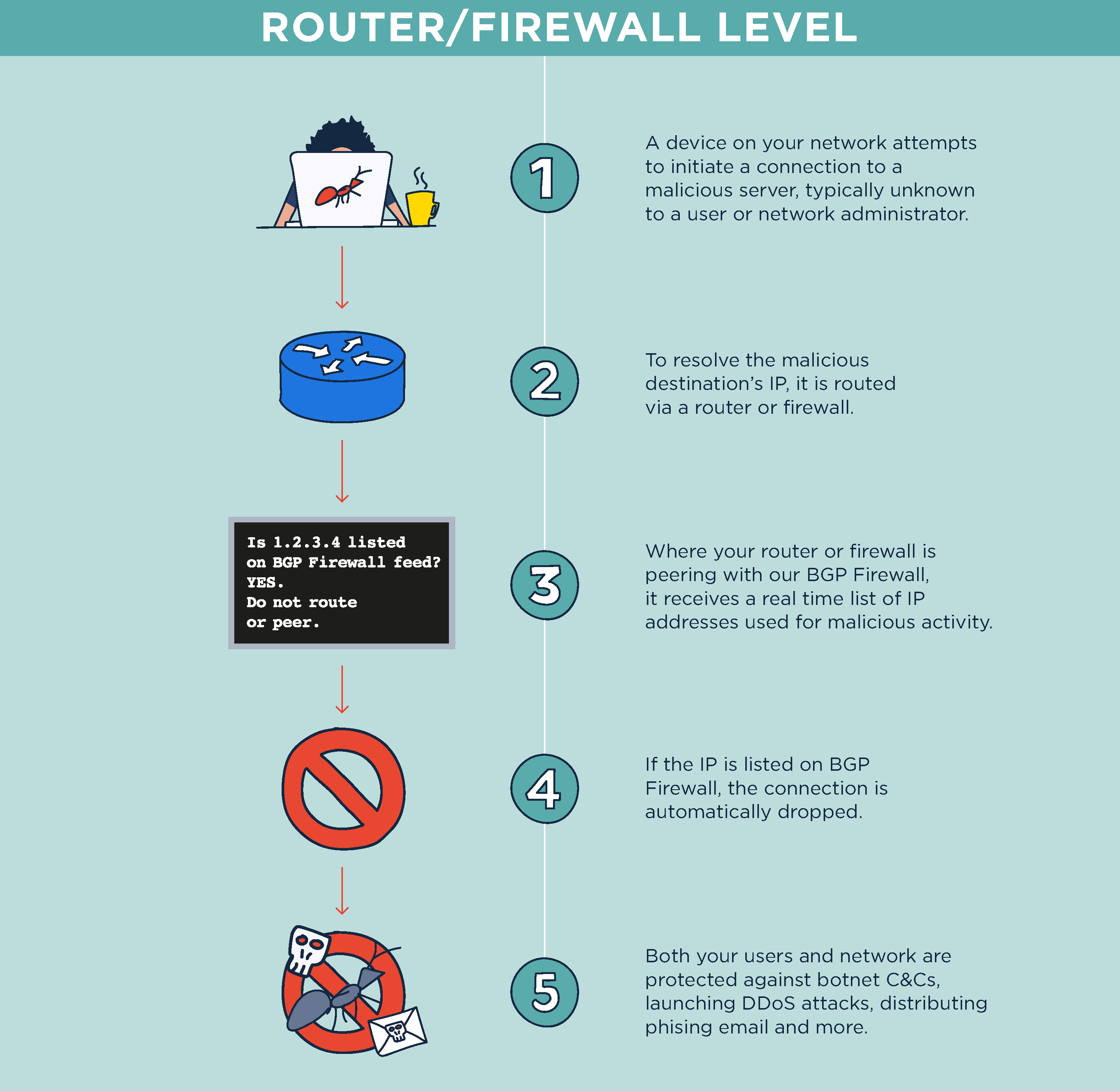
Where BGPF is not utilized, the packet containing the malicious IP continues to be routed to the destination’s web server, and a connection is made to the device. The device is now at risk of malware exfiltrating data and receiving tasks from threat actors, such as those listed above.
You’ll notice in this explanation we’ve focused on outbound network traffic toward botnet C&C servers. It’s important to note that, of course, the connection is blocked both ways. But typically, it’s the infected device initiating the connection (“calling out”) from the user’s perimeter.
How is the user notified of the dropped connection?
At the BGP level, the user typically isn’t notified, which isn’t necessarily a bad thing. An error page can be displayed; however, it’s atypical for these pages to be set up, particularly where the router is ISP-managed.
This isn’t an issue, particularly when talking about attempted connections to a botnet controller, because the user has zero awareness of this attempted connection.
The malware automatically attempts the connection to its botnet C&C without the user’s knowledge. So, where the connection times out and no error page is returned, the user wasn’t expecting anything to the contrary. No harm done.
Now, for the network owner, that’s a different story. This information carries value so that further investigation can be done, as can tracking of the solution’s value. For this, BGP logging should be set up to see what traffic has been blocked. Alternatively, BGP feeds can be set up via your traditional firewall, such as Cisco and Fortinet, which will also log what’s been blocked.
The benefit of protecting at your network edge
Given a user has no active role in this journey, the risk of disgruntled users is dramatically diminished. As is the risk of false positives; with Spamhaus’ BGP Firewall offering, the data is provided with absolute confidence that the IPs listed are indeed malicious. You can find more on this here.
What communities does Spamhaus maintain to block malicious traffic?
We have four communities to protect our users against the most malicious threat actors in real time. And to increase protection further, Spamhaus’ Botnet Controller List (BCL) includes contributions from our data partner, abuse.ch.
One abuse.ch platform, Feodo Tracker, tracks and validates botnet C&C infrastructure connected to the top malware threats. It provides reliable, validated data on botnet C&C infrastructure used by the likes of Emotet and Qakbot; a valuable resource to stay protected.
The four BGP Firewall communities we operate are:
- Don’t Route Or Peer (DROP) – this is a “drop all traffic” list, consisting of the worst of the worse IP space that is either hijacked or leased by cybercriminals. The netblocks listed here are directly allocated by established Internet registries, e.g., Regional Internet Registry (RIR)
- Extended Don’t Route Or Peer (EDROP) – an extension of the DROP dataset but includes sub-allocated netblocks.
- Botnet Controller List (BCL) – Dedicated hosts – IP addresses used to host a botnet C&C server, which controls infected devices. This list only includes single IP addresses (/32) operated with malicious intent, i.e., operated by cybercriminals with the sole purpose of hosting a botnet C&C.
- Botnet Controller List (BCL) – Compromised Hosts – IP addresses of botnet C&Cs hosted on compromised devices, e.g., a threat actor abuses a legitimate user’s device to hosts a botnet C&C on it. This is our newest community; more detail can be found here.
Consumers of this data via Spamhaus get access to technical support, a robust service, and quick resolutions to any perceived false positives that may arise.
Get free protection for 30 days
If you’re interested in seeing how this data performs in your network environment, you can trial the data for free for 30 days here. No payment details are required, and once set up, you’ll immediately gain network protection against the worst of the worst.
BGP Firewall’s best friend – DNS Firewall
They whistle Toy Story’s theme tune – You Gotta Friend In Me…
Now, it’d be remiss to talk about BGP and not mention DNS Firewall, as they perfectly complement each other for the most comprehensive network protection.
So, BGPF is at the router level only and can only process IPs. Critical to stop threat actors that rely entirely on direct IP communication like Emotet, Qakbot, and Dridex. With no domain name used for botnet C&C communication, the router level is the only way to drop and protect against these connections. This modus operandi helps them evade detection.
In the same breath, other threat actors do use domain names for botnet command and control. It does mean they are more likely to get detected. However, if they get caught and the hosting provider takes down the server with the domain’s corresponding IP address, the threat actor can simply move to a new hosting provider. They spin up a new server, point their botnet C&C domain names to it, and they’re back up and running again.
This is where DNS Firewall comes into play. Unlike the router level, at DNS level connections are made with domain names being queried. That also means, where a domain name is used, malicious connections can be blocked before they are being established on the IP level. So DNS Firewall enables additional protection against botnet C&Cs using domain names, while also blocking connections to phishing, malware, adware, and cryptomining.