Content

A recap of some DNS basics
How many phone numbers can you recall? In days gone by, before the advent of the smartphone, most people could remember multiple telephone numbers, as we dialed them manually on a daily basis. Nowadays, with Siri and Alexa making calls for us, it’s difficult to remember one’s mobile number, let alone anyone else’s.
Now imagine if every time you needed to visit a website, you had to recall the relevant internet protocol (IP) address, e.g., 109.147.95.4 (and that’s a short IPv4 address, we won’t even think about an IPv6 one!). Unless you are a numerical savant, such a system wouldn’t be sustainable.
To simplify things, the domain name system (DNS), which is a distributed database, associates domain names with IP addresses, e.g., www.spamhaus.com is associated with 104.18.209.15 & 104.18.208.15. The DNS then operates somewhat like a telephone directory, looking up and connecting with the requested ‘device’ that’s assigned to the IP address in question.
Domain names up for grabs
Registering a domain name is easy. Any available domain name can be registered by anyone, in any part of the world. Well, this isn’t entirely true (nothing is ever simple, is it?). There are certain country-code top-level domains, which have some restrictions on them, but for this article’s sake, let’s not over complicate the narrative!
Most users registering domain names do so for legitimate purposes: business, entertainment, education, hobbies, etc.. However, bad actors abuse the system by registering domain names and using them with the sole purpose of deception, e.g., phishing websites for identity theft and/or financial fraud.
We’ve all heard the stories relating to banking fraud; nefarious individuals register a domain name that closely resembles the bank’s domain name. They build a lookalike website and defraud users into parting with their private banking credentials, and in turn, go off and use these credentials to empty the accounts of their victims.
Bad actors impersonating the Amul brand in India
It’s not only financial services that are open to this kind of abuse. Recently, in India, a spate of domain names have been used to masquerade as popular brands.
Amul, a high-profile dairy brand, went to the Delhi High Court earlier this year in relation to phishing websites. The result was a restraint being placed on various well-known domain registrars selling or offering for sale, any name with “Amul” as a suffix or prefix.
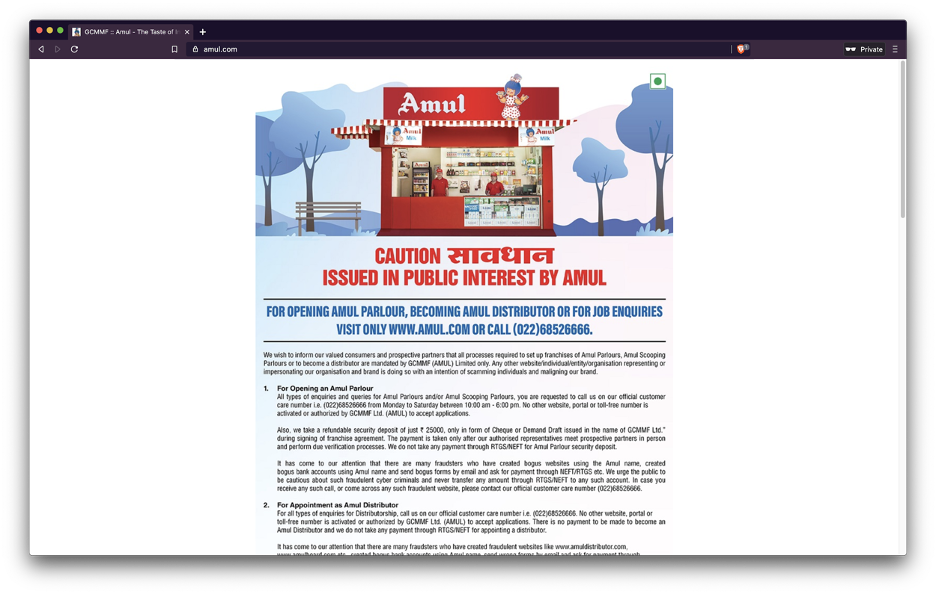
See the legitimate website of Amul.com below, cautioning its audience of websites impersonating the brand for financial fraud.
Meanwhile, also in India, Reliance Retail is also struggling with cybercriminals impersonating their Jiomart brand, an Indian online grocery delivery service. Once again, the focus of this activity is to deceive victims into applying for a franchise. Here’s the legitimate domain name; www.jiomart.com, and here are some of the fake domains created, as reported by The Times of India:
Jiomartfranchiseonline.com
Jiodealership.com
jiomartsfranchises.online
Jiomartfranchies.com
jiomartshop.info
jiomartindia.in.net
Jiomartrelliance.com
jiomartfranchise.co
It’s understandable how victims can easily be fooled into thinking these domain names are part of the legitimate brand.
How can you quickly identify shadow domains?
Brand specialists and marketing teams can utilize Passive DNS to highlight shadow domains or typosquatting and identify entities who are masquerading as their company, brand, or trademark and potentially hurting their customers and damaging their brand.
At a very basic level, Passive DNS is historical data which records the changes in the IP addresses associated with a hostname[1] when a hostname is looked up on the internet. To take a deeper dive into Passive DNS, read this article.
Given the volume and breadth of data recorded, you can see what domains have been observed globally over a period of time. Simply searching a single domain can bring up a wealth of information:
Each of these searches takes less than a minute to run and reveals a wealth of information in one screen, allowing teams to focus on getting the offending domains taken down as quickly as possible, minimizing damage to their brand and reputation.
Why don’t you take a look for yourself, and find out what domains are closely related to your brand, which are not legitimate? Trial Passive DNS for free, with no credit card or payment details required.
1. A hostname is the name of a device connected to the internet